This self-paced course will help you prepare for the Azure Developer certification exam AZ-204: Developing Solutions for Microsoft Azure.


Burp Suite — Web Security Testing is an integrated platform/graphical tool for performing security testing of web applications. Its various tools work seamlessly together to support the entire testing process, from initial mapping and analysis of an application’s attack surface, through to finding and exploiting security vulnerabilities. Burp Suite is installed by default in Kali Linux.
The tool is written in Java and developed by PortSwigger Web Security.
The tool has three editions:
Pricing of the Editions :


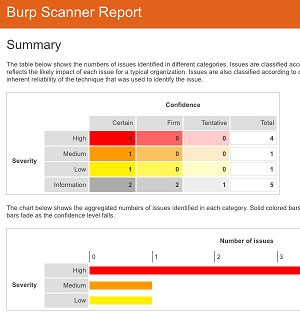
HTML reports
To begin installing Burp Suite visit and select the Get Community option (the third one) to get Burp Suite for free.
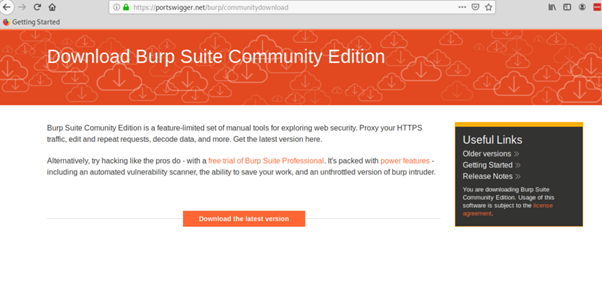
Click on the green Download button.
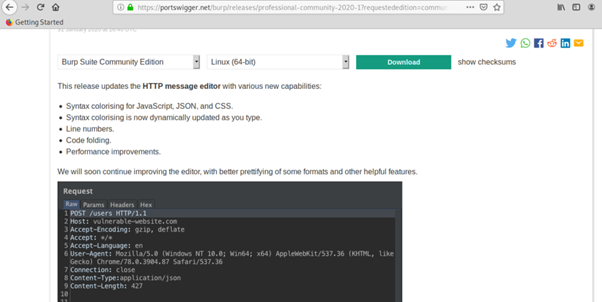
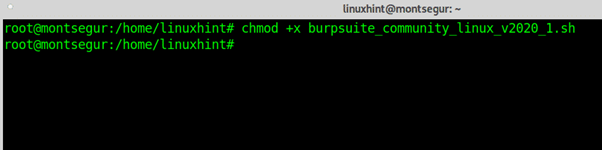
Save the .sh script and give it execution permissions by running:
# chmod +x <package.sh>
In this case for the current version at this date I run:
# chmod +x burpsuite_community_linux_v2020_1.sh
Once the execution rights were given execute the script by running:
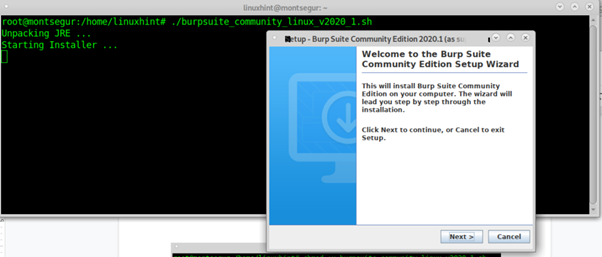
# ./burpsuite_community_linux_v2020_1.sh
A GUI installer will prompt, press on “Next” to continue.
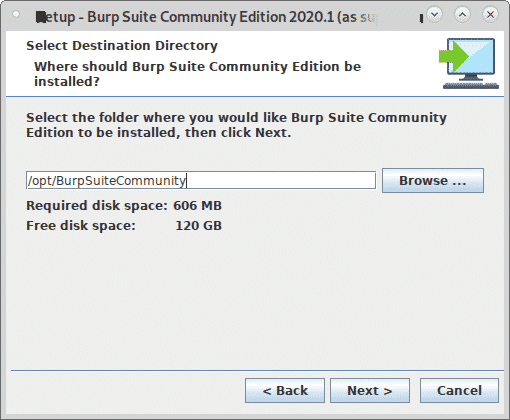
Leave the default installation directory (/opt/BurpSuiteCommunity) unless you need a different location and press Next to continue.
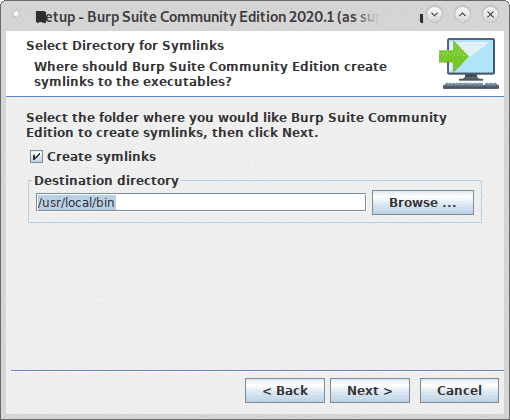
Seek “Create Symlink” selected and leave the default directory and press Next.
The installation process will start. Once the process ends click on Finish.
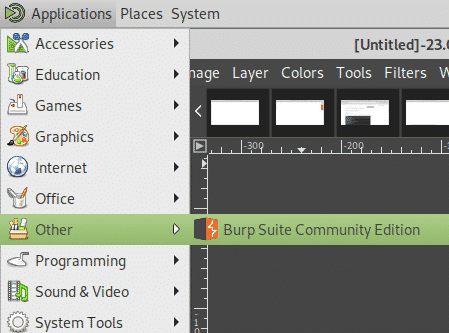
From your X-Window manager apps menu select Burp Suite, in my case it was located on the category “Other”.
Decide if you wish to share your Burp Suite experience or not, click I Decline, or I Accept to continue.
Leave Temporary Project and press Next.
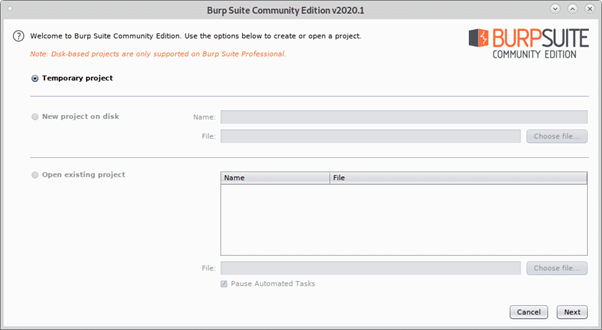
Leave Use Burp defaults and press Start Burp to launch the program.
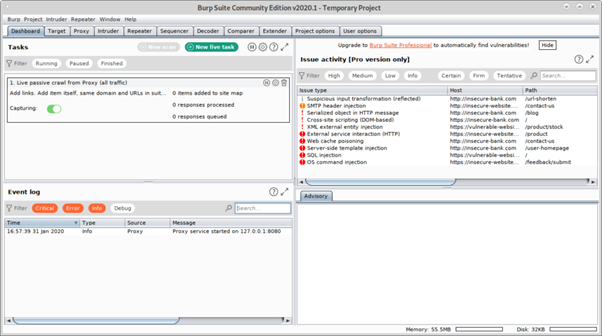
You’ll see Burp Suite main screen:
Before proceeding, open Firefox and open http://burp.
A screen like the shown below will show up, on the upper right corner click on CA Certificate.
Download and save the certificate.
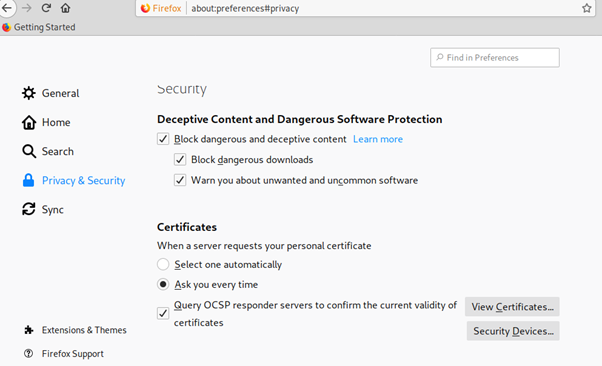
On the Firefox menu click on Preferences, then click on Privacy and Security and scroll down until you find the Certificates section, then click on View Certificates as shown below:
Click on Import:
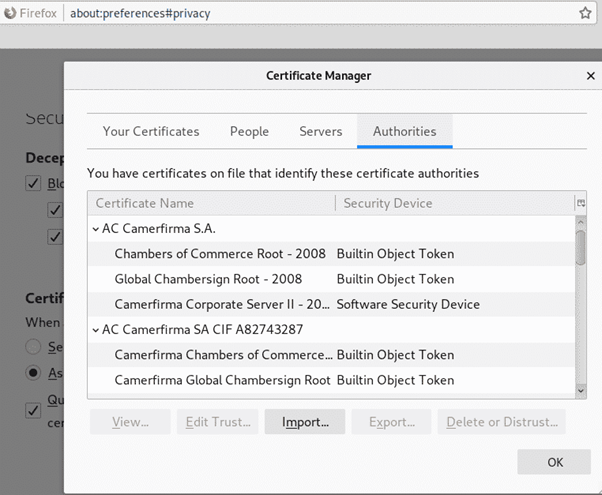
Select the certificate you got previously and press Open:
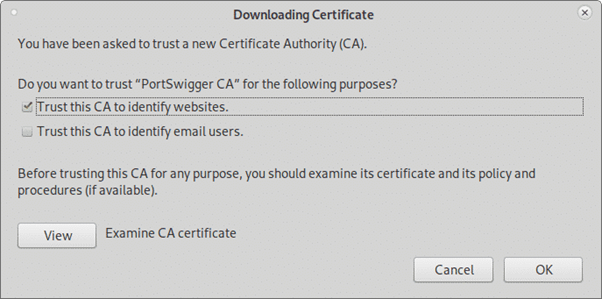
Click on “Trust this CA to identify websites.” and press OK.
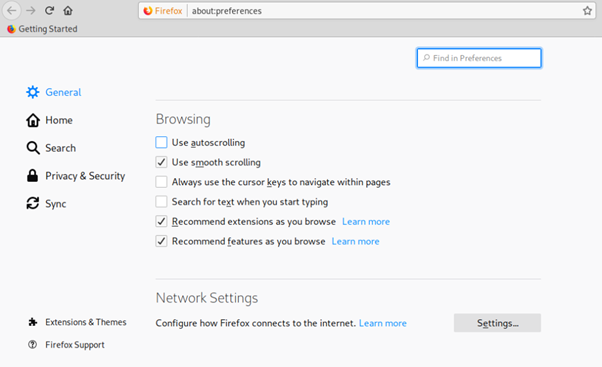
Now, still on the Firefox Preferences menu click on General in the menu located in the left side and scroll down until reaching Network Settings, then click on Settings.
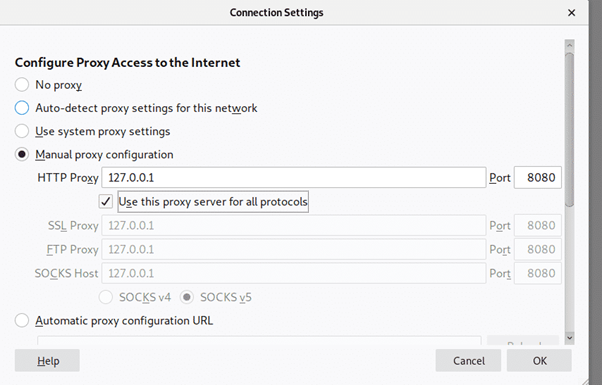
Select Manual Proxy Configuration and in the HTTP Proxy, field set the IP 127.0.0.1, checkmark the “Use this proxy server for all protocols”, then click OK.
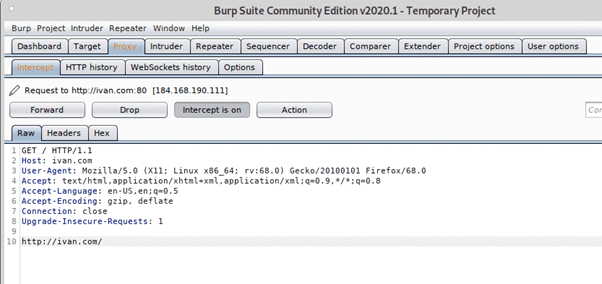
Now Burp Suite is ready to show how it can intercept traffic through it when defined as proxy. On Burp Suite click on the Proxy tab and then on the Intercept sub tab making sure intercept is on and visit any website from your Firefox browser.
The request between the browser and the visited website will go through Burp suite, allowing you to modify the packets as in a Man in the Middle attack.
The example above is the classical Proxy feature show for beginners. Yet, you do not always can configure the target’s proxy, if you did, a keylogger would be more helpful than a Man in the Middle attack.
Now we will use DNS and the Invisible Proxy feature to capture traffic from a system we cannot configure the proxy on.
To begin run Arpspoof (on Debian and based Linux systems you can install with through apt install dsniff) Once installed dsniff with arpspoof, to capture packets from the target to the router on the console run:
# sudo arpspoof -i <Interface-Device> -t <Target-IP> <Router-IP>
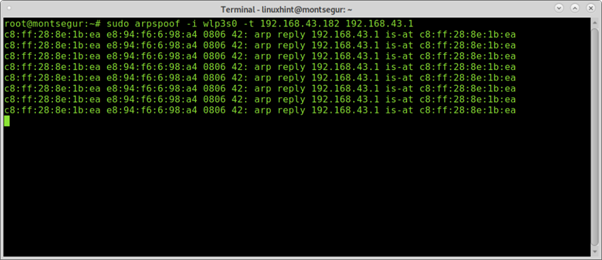
Then to capture packets from the router to the target run in a second terminal:
# sudo arpspoof -i <Interface-Device> -t <Router-IP> <Target-IP>
To prevent blocking the victim enable IP forwarding:
# echo 1 > /proc/sys/net/ipv4/ip_forward
Redirect all traffic to port 80 and 443 to your device using iptables by running the commands below:
# sudo iptables -t nat -A PREROUTING -p tcp — dport 80 -j DNAT — to-destination
192.168.43.38
# sudo iptables -t nat -A PREROUTING -p tcp — dport 443 -j DNAT — to-destination
192.168.43.38
Run BurpSuite as root, otherwise some steps like enabling new proxies on specific ports won’t work:
# java -jar -Xmx4g /opt/BurpSuiteCommunity/burpsuite_community.jar
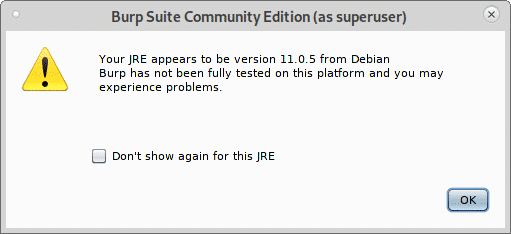
If the following warning appears press OK to continue.
Once BurpSuite is open, click on Proxy>Options and click on the Add button.
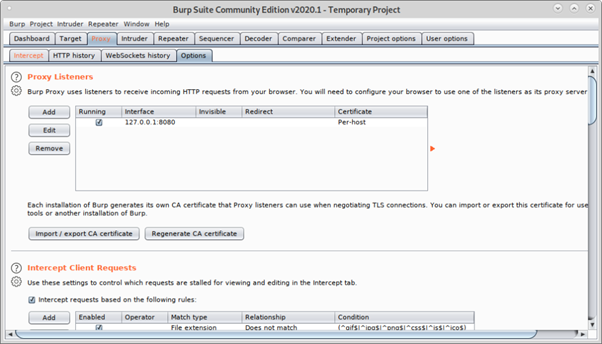
Select 80 and on Specific address select your Local network IP address:
Then click on Request handling tab, checkmark Support Invisible proxying (enable only if needed) and press OK.
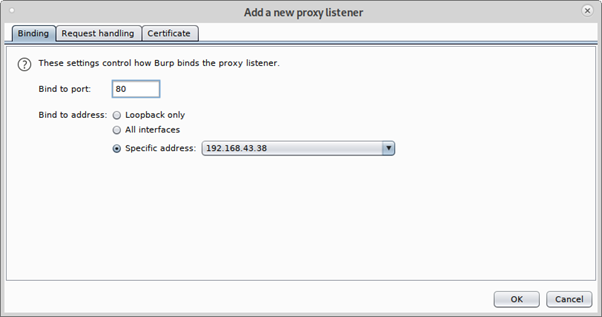
Repeat the steps above now with port 443, click on Add.
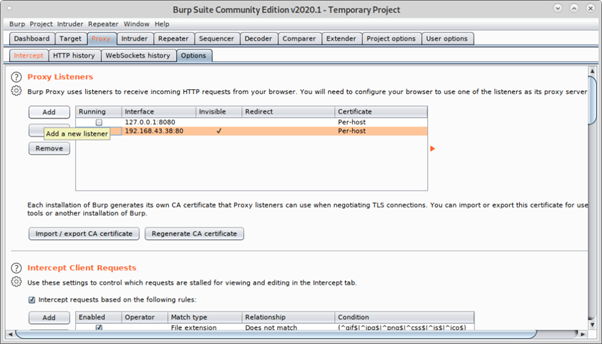
Set the port 443 and again select your local network IP address.
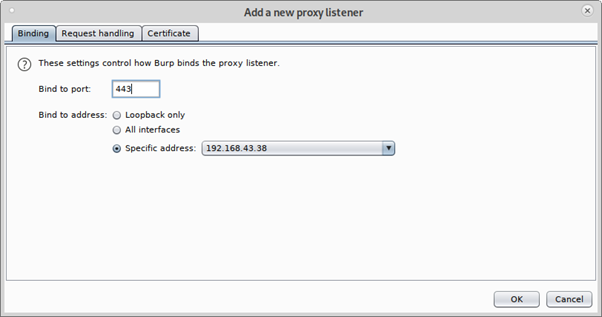
Click on Request Handling, checkmark support for invisible proxying and press OK.
Mark all proxies as running and as invisible.
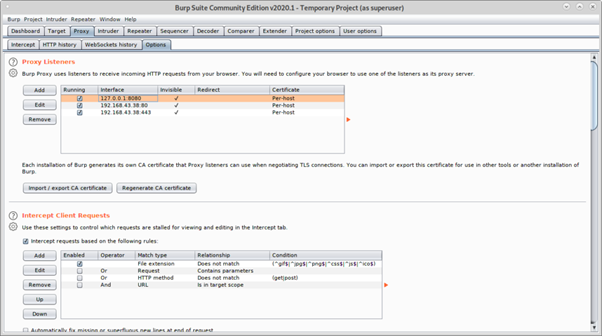
Now from the target device visit a website, the Intercept tab will show the capture:
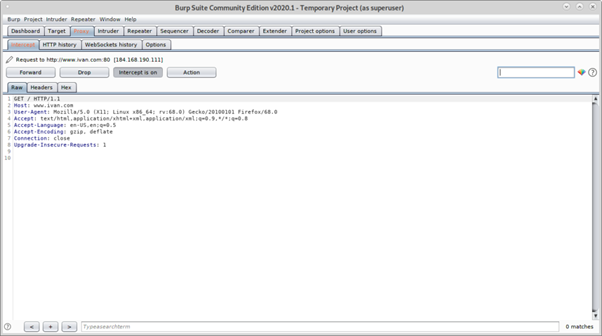
As you can see you managed to capture packets without previous proxy configuration on the target’s browser.

This self-paced course will help you prepare for the Azure Developer certification exam AZ-204: Developing Solutions for Microsoft Azure.
Hi there! Would you mind if I share your blog with my Facebook group?
There’s a lot of people that I think would really enjoy your content.
Please let me know. Thanks
I like the valuable info you provide in your articles.
I’ll bookmark your weblog and check again here frequently.
I am quite certain I will learn plenty of
new stuff right here! Good luck for the next!
Everything is very open with a very clear description of
the issues. It was really informative. Your site is very useful.
Thank you for sharing!
This post will help the internet people for building up new webpage or even a weblog from start
to end.
Check out my web blog … CáCh ChơI Keno
Very good article. I will be facing some of these issues as well..