This self-paced course will help you prepare for the Azure Developer certification exam AZ-204: Developing Solutions for Microsoft Azure.


Azure WebApp Auto Healing Policy is a feature to auto-heal your service whenever it detects anomaly with the service. Auto-Healing allows you to restart, log, or perform custom actions (action) whenever certain criteria about your App Service are met (trigger), for example, recycling service when slow requests are detected.

· Most of the time your apps are running healthily and happily. However, sometimes your app may run into issues, resulting in downtime, slowness, or other unexpected behaviors.
· App Service Diagnostics to help you diagnose and solve issues with your web app with recommended troubleshooting and next steps.
· However, these unexpected behaviors may be temporarily resolved with some simple mitigation steps, such as restarting the process or starting another executable, or require additional data collection, so that you can better troubleshoot the ongoing issue at a later time.
· This new Auto Healing experience in App Service Diagnostics. With our new Auto Healing tile shortcut, you can set up custom mitigation actions to run when certain conditions (that we define as unexpected or a sign of unhealthy behavior) are met.
· Currently, this new experience is only for Windows web apps for now.
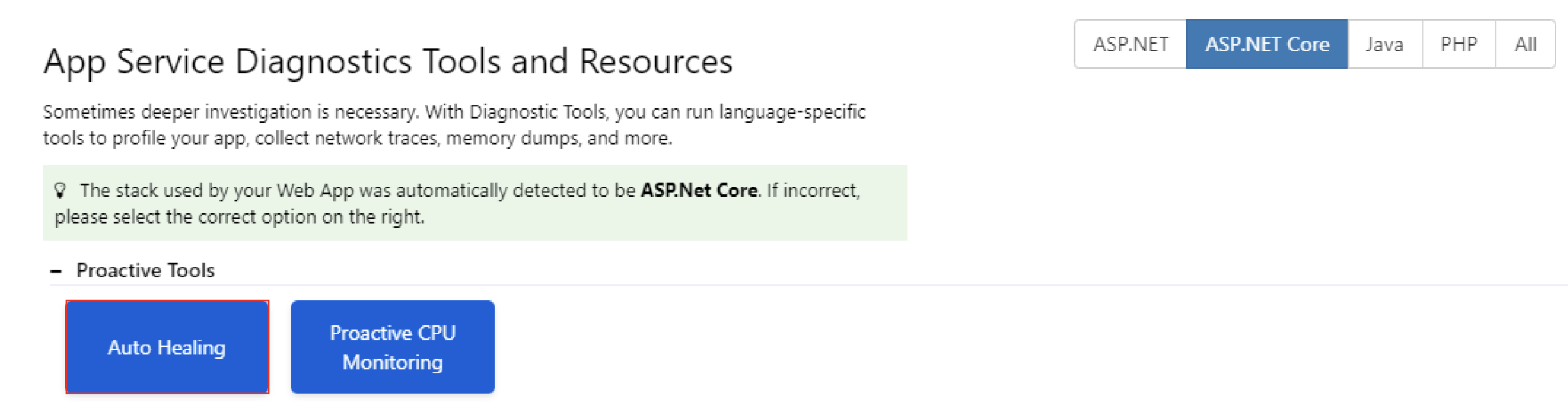
· Click Diagnostic Tools from the App Service Diagnostics homepage.
. Then from inside it click on the Auto Healing to go into the screen

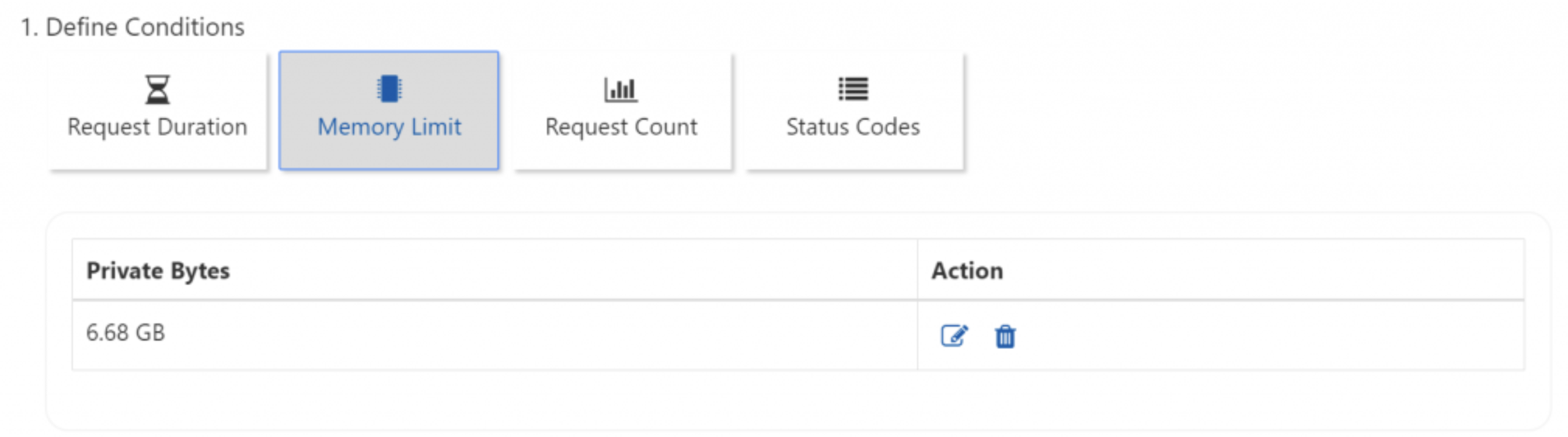
Step 1: Define conditions Select the tile that best matches the condition that you want to set for your mitigation rule. The conditions that are supported with the new Mitigate/Auto Heal experience in App Service Diagnostics are:
After reading the description, select the blue button to configure the rule parameters. Parameters that have a red asterisk next to it are required fields
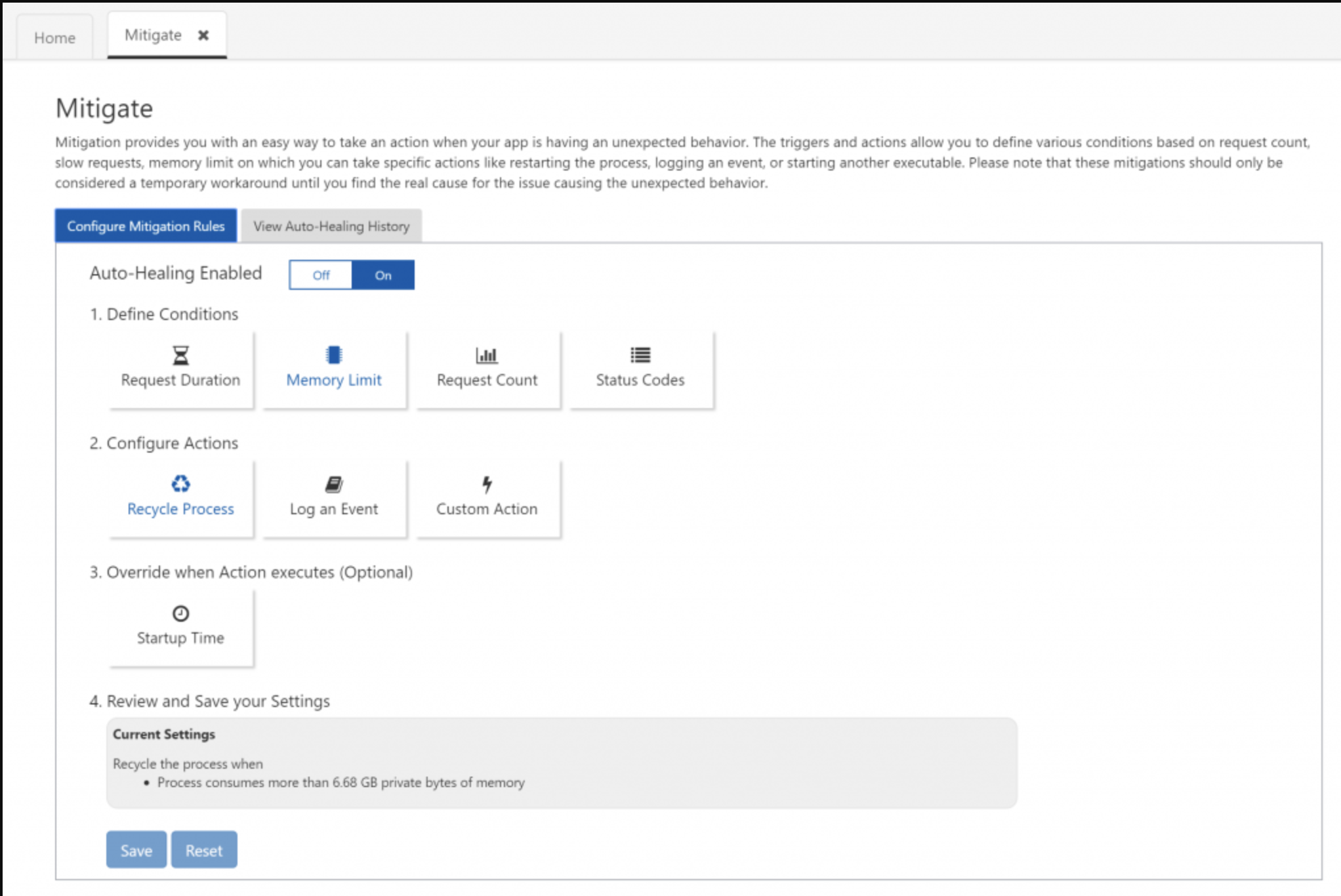
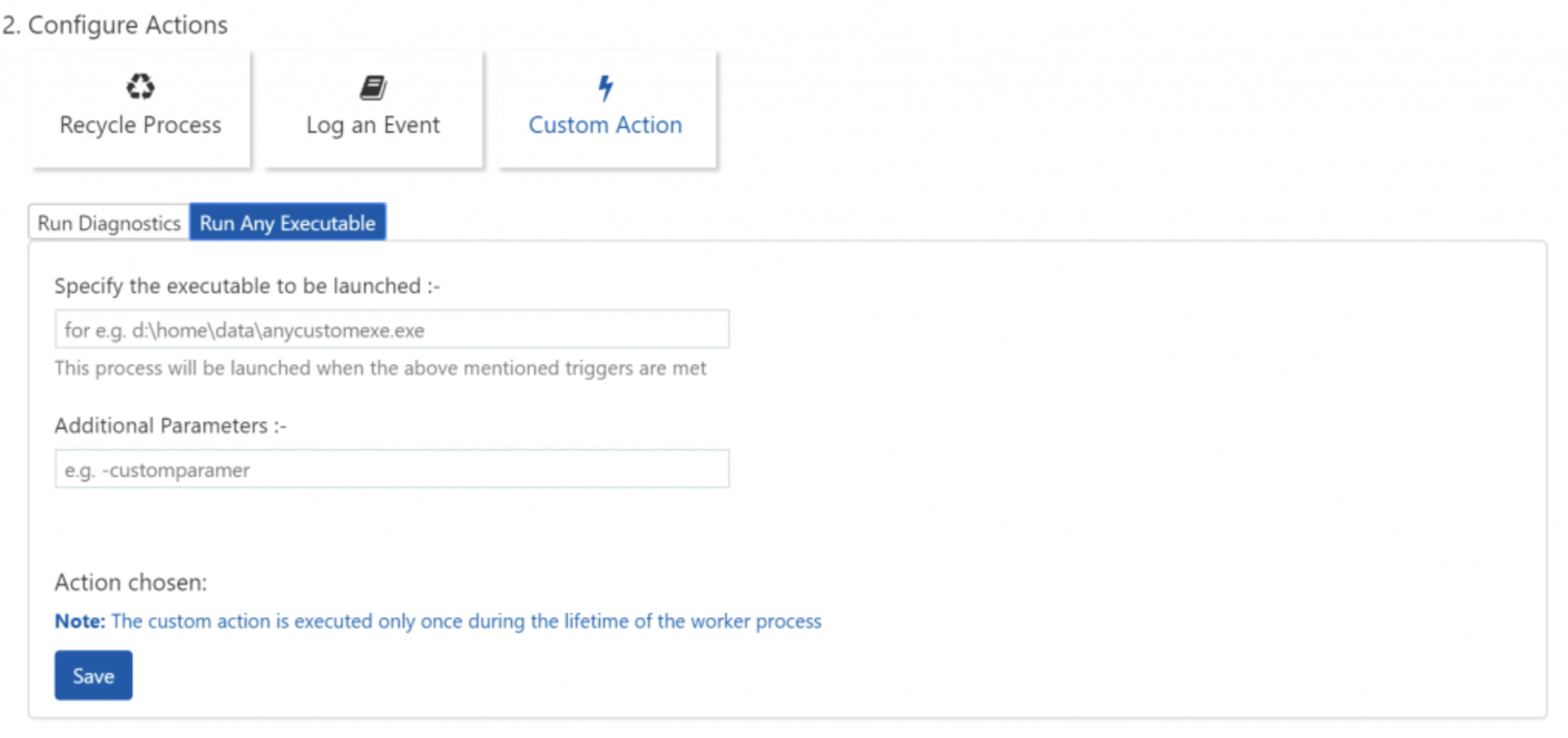
Step 2: Configure actions Select the tile that best matches the auto-heal mitigation action that you want to perform under your mitigation rule conditions. When the graphic is blue, it means that action has been selected. (For custom actions, be sure to fill out the parameters required). The custom mitigation actions that are supported are:
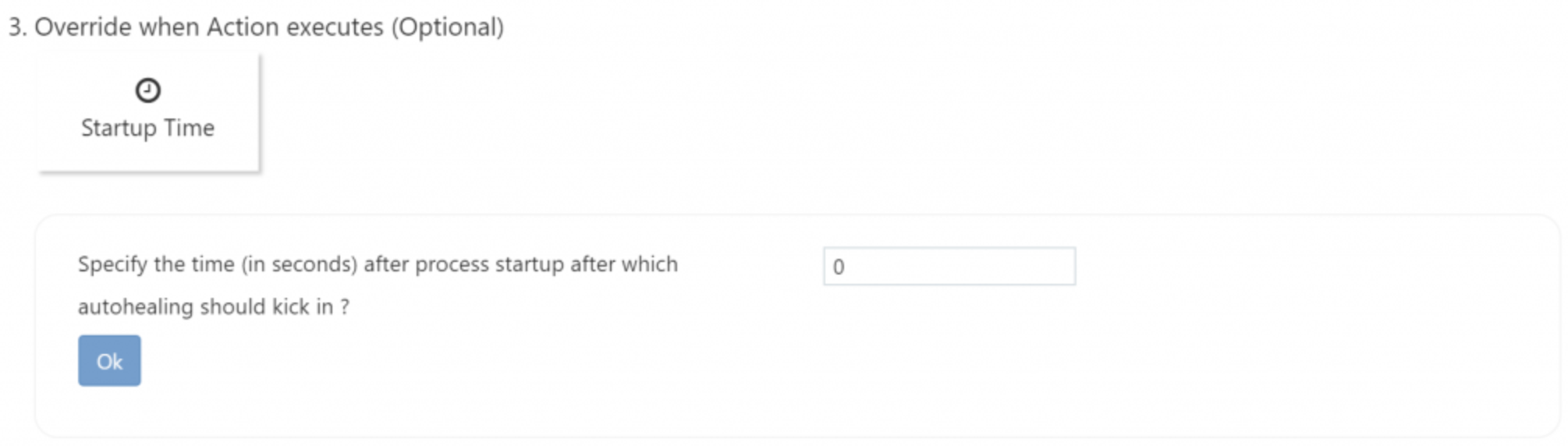
Step 3: Override when action executes (optional) Sometimes when an app has a long startup time, depending on the mitigation rule conditions that are set, it may kick off the mitigation action during app startup, which is not the intended use case. By modifying the startup time, you can specify how much time the mitigation rule should wait after the process startup before the mitigation rule kicks off.
Step 4: Review and save your settings Here, you can review the rules that you just created and save them. If you have previously defined rules, they will show up under Current Settings (no rules will show up under Current Settings until they are saved). Saving mitigation settings will restart the application domain for the web app and this can cause logged-in user information, sessions, and in-memory cache to be cleared. Hence, it is advised to make these changes during non-business hours. Two things to keep in mind:
· For the mitigation rule that you want to delete, select the condition that the rule is set on. Then, click on the trash can next to the rule that you configured.

This self-paced course will help you prepare for the Azure Developer certification exam AZ-204: Developing Solutions for Microsoft Azure.