This self-paced course will help you prepare for the Azure Developer certification exam AZ-204: Developing Solutions for Microsoft Azure.


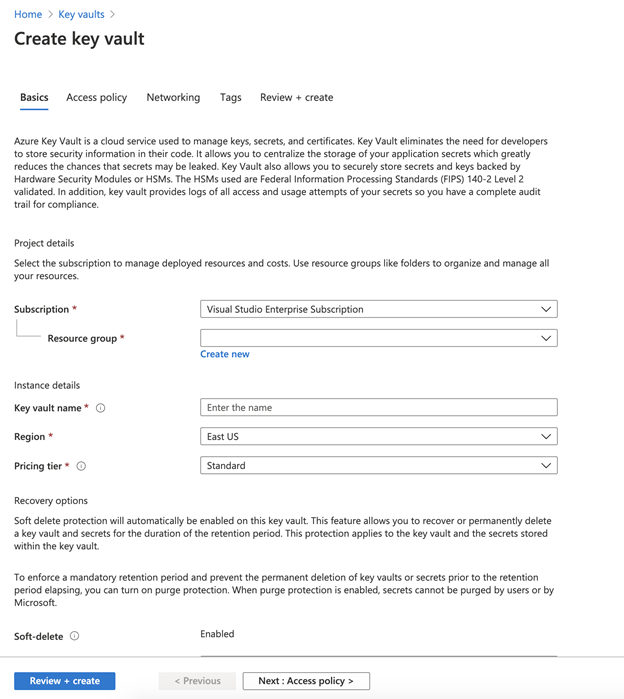
In this blog, you will learn how to Configure Azure DevOps Pipeline with Azure Key Vault to securely store and manage sensitive information such as keys, passwords, certificates, etc.
It is a centralized storage which are safeguarded by industry-standard algorithms, key lengths, and even hardware security modules.
This prevents the disclosure of information through source code, a common mistake that many developers make.

Many developers leave confidential details such as database connection strings, passwords, private keys, etc., in their source code which when gained by malicious users can result in undesired consequences.
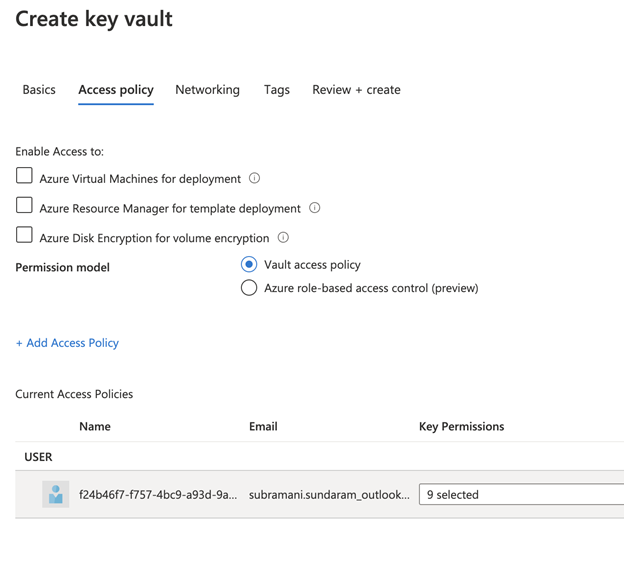
Access to a key vault requires proper authentication and authorization and with RBAC, teams can have even fine granular control who has what permissions over the sensitive data.

Below are the tasks that we need to do:
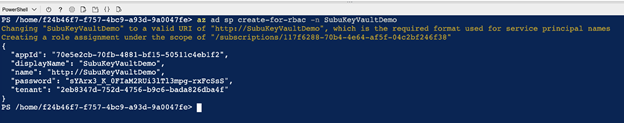
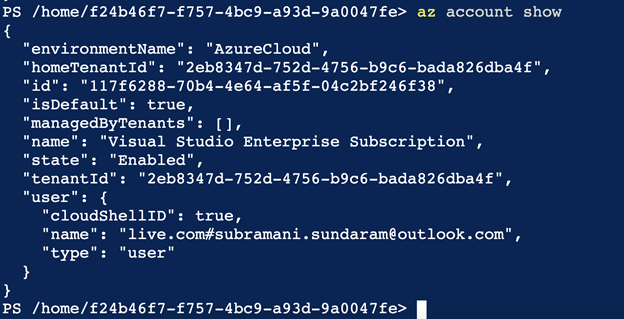
We will need a service principal to deploy an app to an Azure resource from Azure Pipelines.
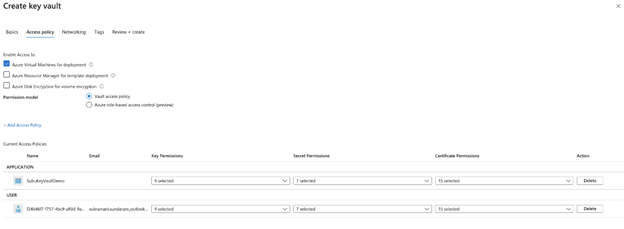
We are going to retrieve secrets in a pipeline, we will need to grant permission to the service when we create the key vault.
A service principal is automatically created by Azure Pipeline when you connect to an Azure subscription from inside a pipeline definition or when you create a new service connection from the project settings page.
We can also manually create the service principal from the portal or using Azure CLI, and re-use it across projects.
We need to add our newly created service principal to the Access policy of the Key vault and also we need to enable that Azure virtual machine check box which is showing below.

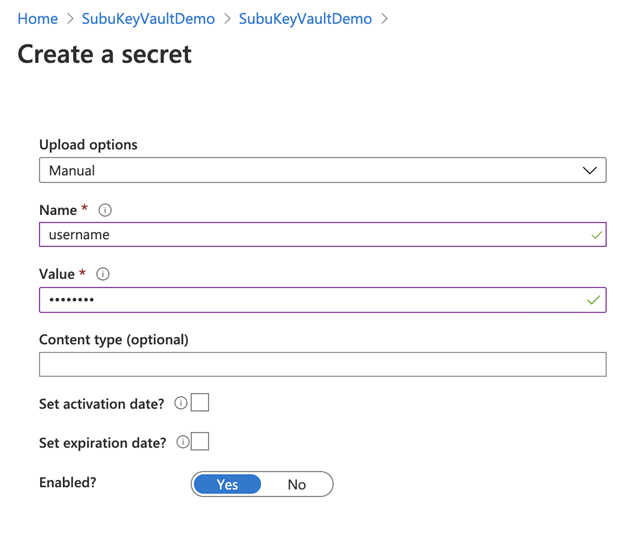
Now we need to add the secrets such as username and password that is required for the virtual machine creation.
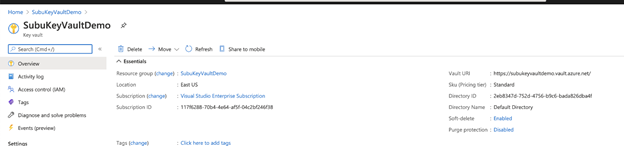
Now our work on the Azure side is completed . We need to now proceed towards the Azure DevOps side now.
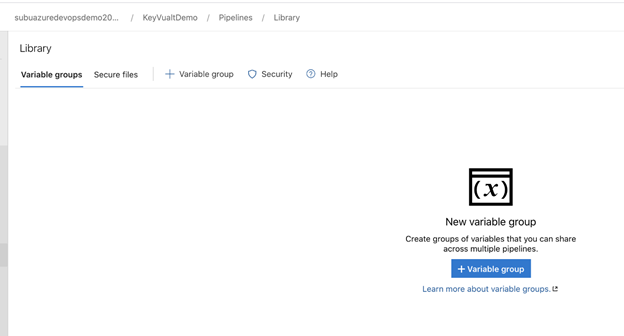
Including these secrets of Key vault in Azure Libraries:
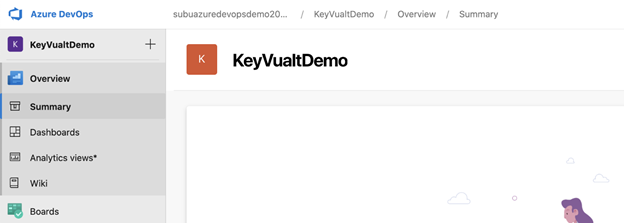
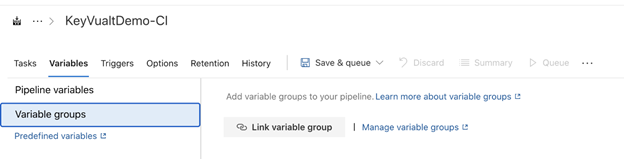
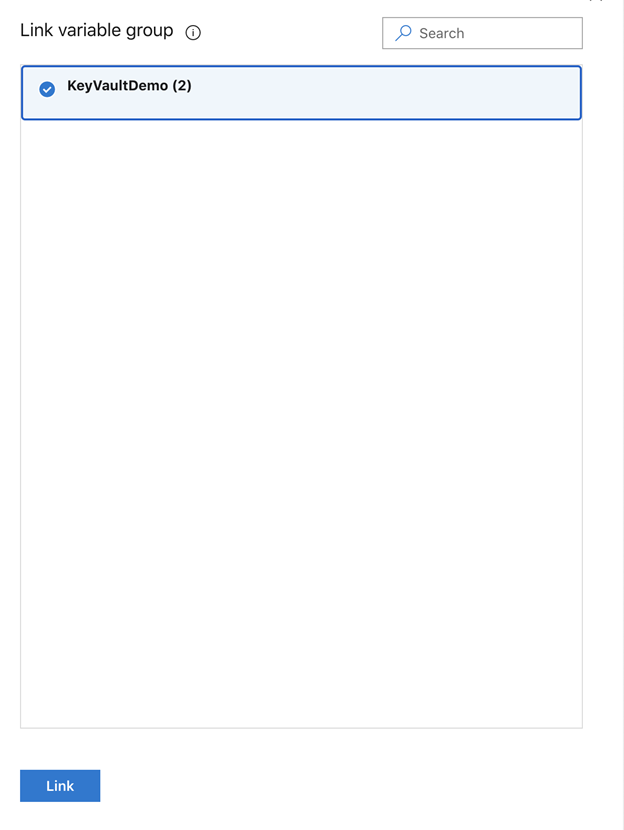
3. Go to the Libraries and then add this key vault to the Azure DevOps.
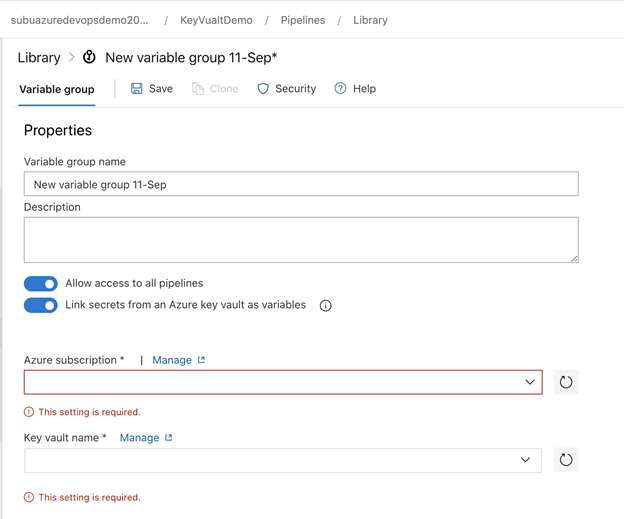
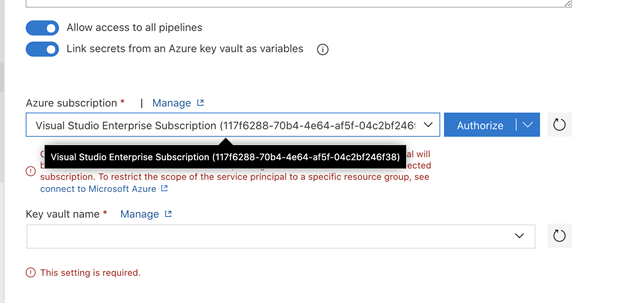
We need to authorize it so that Azure DevOps and the Key vault are linked together, then whatever the username and password that we added in the key vault will be linked here.
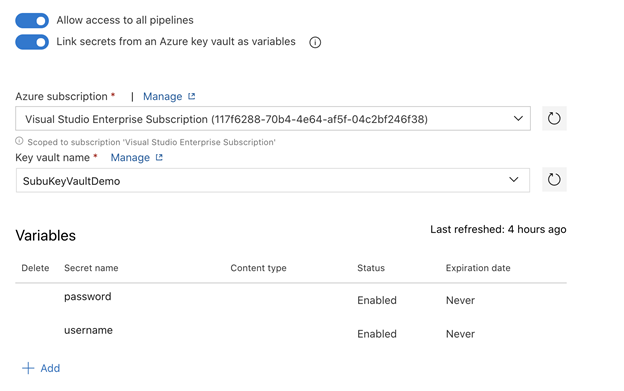
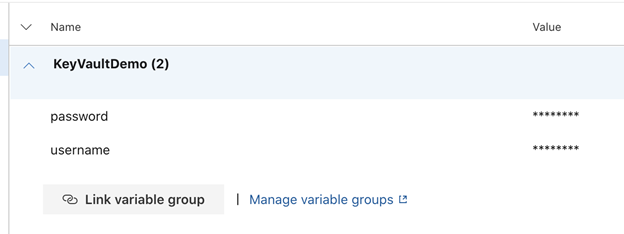
So, by this way the Keys and secrets that we have added will be reflected here and now we are ready to use it as part of the pipeline.
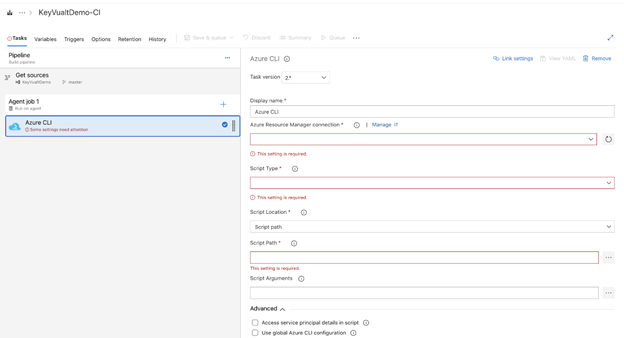
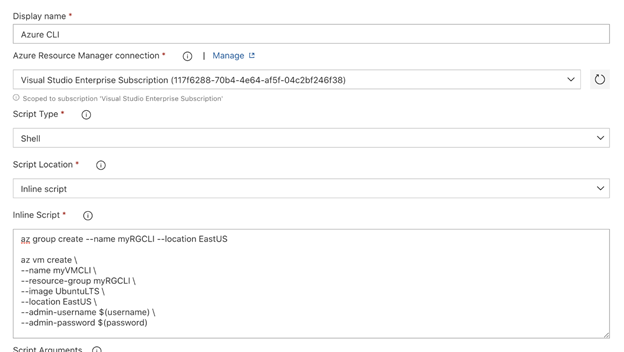
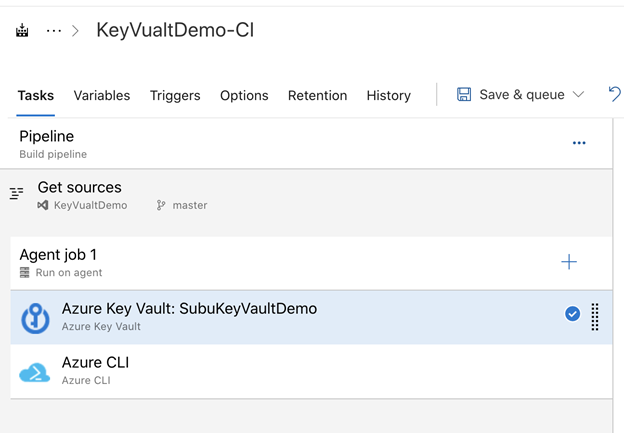
Now, we have added the username and password of the VM as a variable and now we need to go to the variable section and add the key vault to this pipeline.
Now , we are good to start the pipeline and this username and password will be automatically taking the values from the key vault and run it.
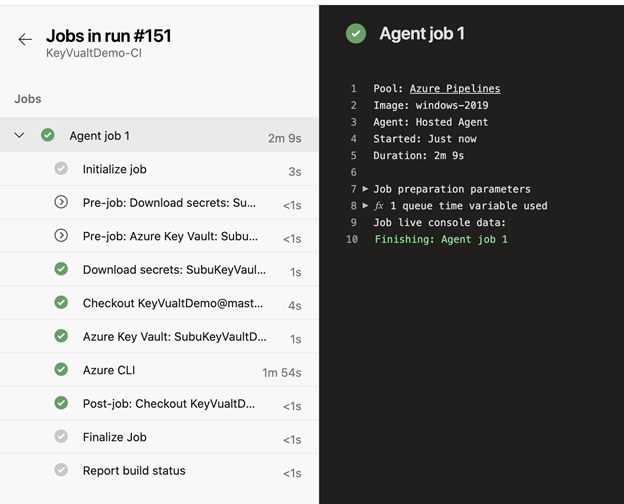
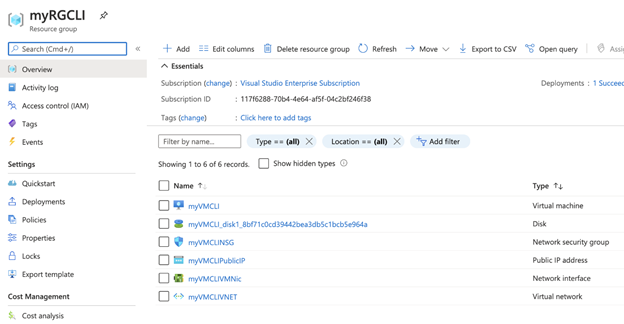
Now, we are going to check it from Azure side that if the VM is created or not.
So, in this blog you have learnt how to Configure Azure DevOps Pipeline with Azure Key Vault. This way we can secure the secrets and keep all the secrets in a centralized location.
For any training related to Microsoft Azure, please contact us here

This self-paced course will help you prepare for the Azure Developer certification exam AZ-204: Developing Solutions for Microsoft Azure.